Job
- Level
- Senior
- Job Field
- IT, Security
- Employment Type
- Full Time
- Contract Type
- Permanent employment
- Salary
- 4.000 to 5.200€ Gross/Month
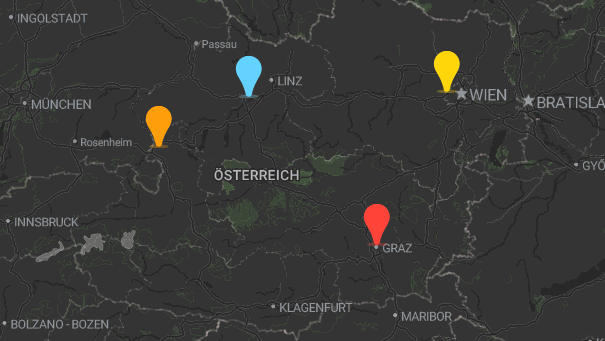
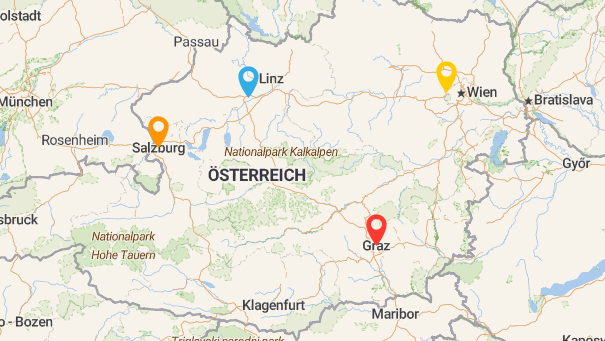
- Location
- Salzburg, Graz, Wels, Vienna
- Working Model
- Hybrid, Onsite
Job Summary
In this role, you analyze security alerts, conduct incident response measures, and proactively hunt threats while closely collaborating with detection engineering to enhance security rule sets.
Job Technologies
Your role in the team
- Incident Detection & Analysis: Analysis and assessment of security alerts and incidents within the SOC, as well as prioritization and initiation of appropriate measures for quick and effective response.
- Incident Response: Execution and coordination of incident response measures including containment, eradication, and recovery, as well as documentation and post-incident review of security incidents.
- Threat Hunting: Proactive identification of threats through hypothesis-driven Threat Hunting based on current TTPs, Threat Intelligence, and MITRE ATT&CK.
- Use Case Feedback & Detection Improvement: Close collaboration with Detection Engineering to improve existing Detection Rules and develop new Use Cases based on Incident Learnings.
- SIEM & Tooling Usage: Active work with SIEM and security tools (e.g., Elastic Security) for analysis, correlation, and visualization of security-related events.
- Customer Communication & Reporting: Communication of incidents, risks, and measures to internal stakeholders and customers, as well as the preparation of reports and recommendations.
- Quality & Development: Continuous improvement of analysis processes, playbooks, and SOC workflows, as well as mentoring less experienced analysts.
This text has been machine translated. Show original
Our expectations of you
Education
- Completed technical education (HTL, FH, university) or equivalent qualification, as well as several years of experience in Security Operations, SOC, or Incident Response.
Qualifications
- Basic knowledge of scripting or automation (e.g., Python, APIs) is advantageous.
- Analytical, structured, and solution-oriented working style as well as strong communication skills in German and English.
Experience
- Extensive hands-on experience in the analysis and handling of security incidents within a SOC environment.
- Very good understanding of attack vectors, TTPs, and common threat scenarios, as well as experience with frameworks such as MITRE ATT&CK.
- Experience with SIEM and security tools (e.g., Elastic Security) as well as proficient handling of log analysis from Windows, Linux, and network sources.
- Experience in Threat Hunting as well as in developing hypotheses for identifying complex attacks.
- Experience in structured incident documentation as well as in reporting to clients or management.
This text has been machine translated. Show original
What we offer
- Your gross salary according to the collective agreement ranges between EUR 4,000 and EUR 5,200.
- A salary adjustment is planned depending on qualifications and professional experience.
This text has been machine translated. Show original
Benefits
More net
Food & Drink
Health, Fitness & Fun
Work-Life-Integration
Topics that you deal with on the job
Job Locations
This is your employer

x-tention Informationstechnologie GmbH
Klagenfurt Am Wörthersee, Graz, Salzburg, St. Peter In Der Au, Wels, Wien
Our company provides expert consultation, software development, and operational management for information systems in the health care and social services industries—from large hospitals to smaller organizations.
Description
- Company Type
- Established Company
- Working Model
- Hybrid, Onsite
- Industry
- Healthcare, Social Sector, Internet, IT, Telecommunication
Dev Reviews
by devworkplaces.com
Total
(3 Reviews)3.9
Workingconditions
4.0Culture
3.9Career Growth
4.2Engineering
3.5